Tech Support Scams
What are tech support scams?
Technical support scams are common worldwide, and scammers often use similar approaches to deceive innocent people. Typically, they impersonate companies like Apple, Microsoft, Google etc, and contact individuals about a computer virus, technical issue, or security concern. Their goal is to instill fear and urgency, prompting victims to seek their assistance or pay for fake services. The scammers offer to "fix" the issue and trick individuals into revealing personal information or use other tactics to steal their money. Globally, fake technical support scams have been reported in many countries including, Canada, United States, Ireland, United Kingdom, The Netherlands, Germany, Australia, New Zealand, India, and South Africa, among others.
How to identify fake technical support calls?
The scammers pretend to call or email from companies like Microsoft, Apple etc “trying” to fix a non-existent issue. Sometimes, they even send pop-up messages that seem to come from a legitimate source — all to extract sensitive information from uninformed individuals.
Last year in the US, a retired accountant from Brooklyn, New York lost $100,000 in a tech support scam. Scammers called her after her laptop froze and told her they owed her a refund of $10 for the premium she paid for antivirus, which failed because of them. The scammer faked a mistaken deposit and pressured her to return the money. The woman could not figure out that it was her own funds transferred between accounts. She was asked to return the money in cash, and a code word was given to her. She withdrew the cash and handed it to a courier using the secret code word. It was much later that she realized it was all an elaborate scam.
Most online scams rely on fear and urgency to steal money or sensitive information from victims. This tactic is also commonly used in phone scams by fake IT support. Scammers call people about a virus or tell them their system has been hacked, causing individuals to act out of fear without thinking rationally.
Do not install any remote access software on your device upon scammers’ insistence. Common remote access programs include AnyDesk and TeamViewer. Cybercriminals pressure you to install these, saying they will "fix" your computer, but their real intent is to steal your information.
To stay off the police radar, scammers often request payment through gift cards, cryptocurrencies, or wire transfers. Stay alert and be cautious if you receive such a request.
If a tech support representative calls you about a lucrative refund, verify its legitimacy through reliable channels. Similarly, if you receive a call about an accidental transfer of funds with a request for repayment, consider it a red flag. Also, keep in mind that legitimate tech support will never demand payments through gift cards or wire transfers.
Be cautious of warning messages on your devices that say your device has a virus, has been hacked, or has a security concern. These messages are designed to create fear and pressure you into taking immediate action.
What to do if you are a victim of a tech support scam?
If you have fallen victim to a technical support scam, take these actions as soon as you can to minimize damage:
- Contact your bank: Immediately contact your bank and inform them about all the transactions you have made. Keep screenshots and receipts ready, if any. Keep monitoring your account and report any questionable activity.
- Stop all communications with the scammer: As soon as you realize you have been scammed, stop communicating with the scammer. They might try to lure you into giving more money by pretending to help you.
- Disconnect internet: If you have provided remote access to your device, it is important that you disconnect the internet to avoid any further loss.
- Check for suspicious software on your device: Uninstall any app you do not recognize and run a security scan using a trusted antivirus software.
- Change your passwords: Change passwords for all important accounts, including banking and social media.
- Gather evidence: Keep records of phone calls, emails, and text messages to provide to the relevant authorities for investigation and potential blocking of the money transfer.
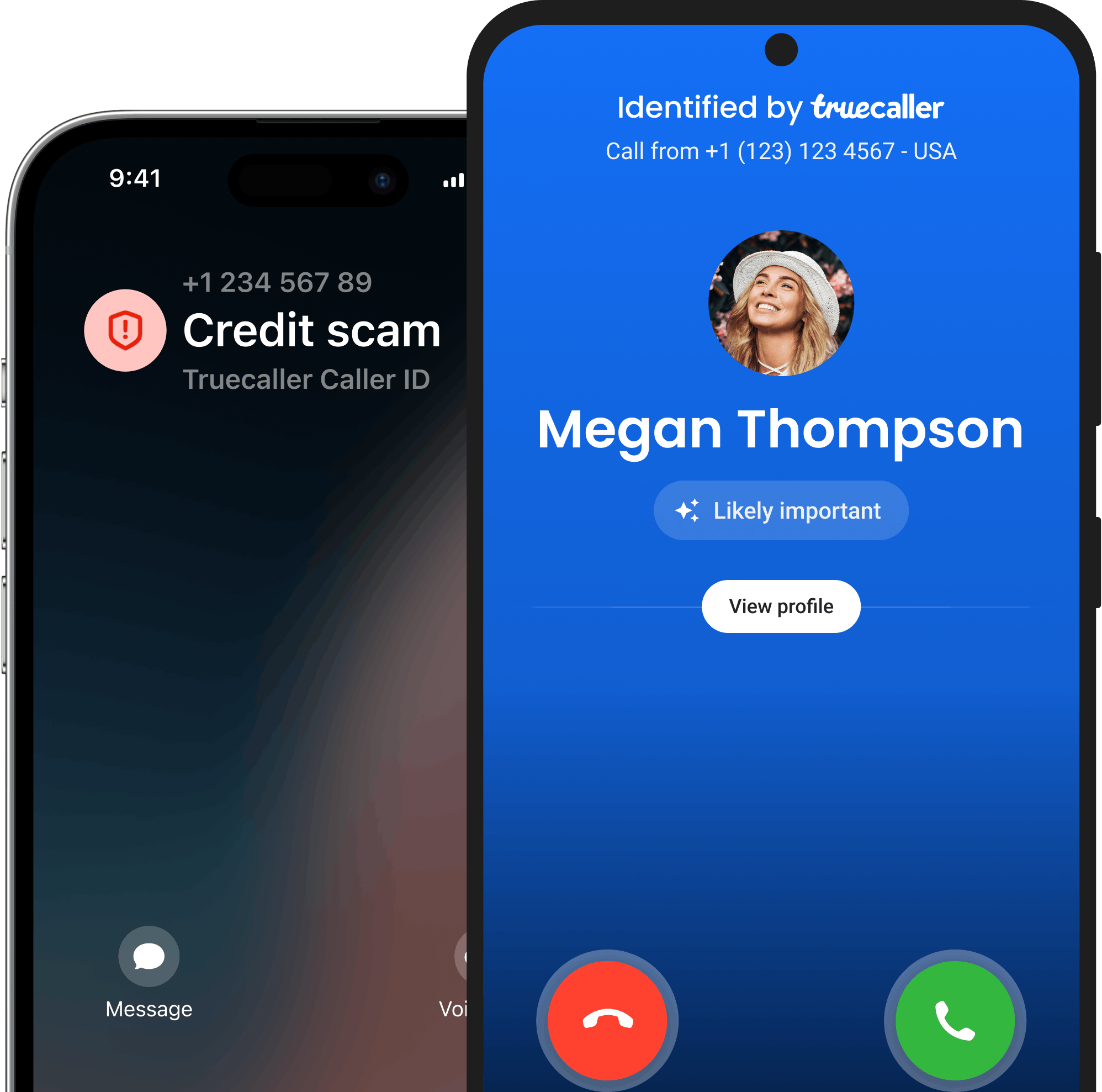
- Report the number on the Truecaller app: Since Truecaller is a community-based platform, reporting helps warn and protect others from scammers.
Country wise reporting authorities for Deepfake Scams
If you are in the United States, these could be some agencies you could reach out to:
- Federal trade commission: https://consumer.ftc.gov/features/pass-it-on/charity-fraud
- Internet crime complaint centre: https://www.ic3.gov/
Reporting the scam on Truecaller will help prevent others from becoming victims.
- For immediate assistance and guidance on cyber fraud, call 1930 (toll-free)
- Serious Fraud Investigation Office: https://sfio.gov.in/
- Chakshu - Report suspected fraud communication:
https://services.india.gov.in/service/detail/chakshu-report-suspected-fraud-communication
- Sanchar Saathi: https://sancharsaathi.gov.in/sfc/Home/sfc-complaint.jsp
Reporting the scam on Truecaller will help prevent others from becoming victims.
- Police Special Fraud Unit (PSFU)
Email: report@specialfraudunit.org.ng, pro@specialfraudunit.org.ng
Whatsapp: 08127609914
Voice Call/SMS: 07082276895
Social Media: Facebook - Economic and Financial Crimes Commission (EFCC)
Email: info@efcc.gov.ng
Phone number: +234 8093322644, +234 (9) 9044751
Social Media: Facebook, Twitter, Instagram - Independent Corrupt Practices Commission (ICPC)
Email: info@icpc.gov.ng
Phone number: 08076369259, 08076369260
Social Media: Instagram, Twitter, Facebook
Reporting the scam on Truecaller will help prevent others from becoming victims.
- Action fraud: https://www.actionfraud.police.uk/charities
- Fundraising regulator: https://www.fundraisingregulator.org.uk/complaints
- GOV.UK: https://www.gov.uk/report-suspicious-emails-websites-phishing
- National cyber security centre: https://www.ncsc.gov.uk/
Reporting the scam on Truecaller will help prevent others from becoming victims.
- CSA Singapore: https://www.csa.gov.sg/cyber-aid
- File a police report at https://eservices1.police.gov.sg
Reporting the scam on Truecaller will help prevent others from becoming victims.
- Scamwatch: https://www.scamwatch.gov.au/
- Email: ReportScams@ato.gov.au
- Scam helpdesk: https://www.servicesaustralia.gov.au/phone-us?context=64107#scams
Reporting the scam on Truecaller will help prevent others from becoming victims.
- South African Fraud Prevention Service: https://cybercrime.org.za/reporting
- Internet Service Providers’ Association (ISPA): https://ispa.org.za/safety/report-cybercrime/
- In case of SIM fraud, please contact your mobile service provider
Reporting the scam on Truecaller will help prevent others from becoming victims.
- Online: Cybercrime Investigation Unit (Korean National Police Agency) https://cyberbureau.police.go.kr/eng/index.do
- Phone: 182
- Korea Internet & Security Agency (KISA) – Cyber Incident Response Center: https://www.krcert.or.kr
- Phone: 118 (Cybercrime and Online Fraud Hotline)
Reporting the scam on Truecaller will help prevent others from becoming victims.
- Office of cybercrime: https://cybercrime.doj.gov.ph/contact-us-2/
- Email: cybercrime@doj.gov.ph
- National Bureau of Investigation (NBI) – Cybercrime Division: https://nbi.gov.ph/
- Philippine National Police (PNP) – Anti-Cybercrime Group: https://acg.pnp.gov.ph/
Reporting the scam on Truecaller will help prevent others from becoming victims.
- Crime Victims Helpline: 116 006 (free)
- Crimestoppers: 1800 250 025
- Local police
Reporting the scam on Truecaller will help prevent others from becoming victims.
- National Cyber Security Centre (NCSC): https://english.ncsc.nl/contact
- Phone: +31 70 751 55 55
- Local police station
Reporting the scam on Truecaller will help prevent others from becoming victims.
- Federal Criminal Police Office (Bundeskriminalamt - BKA): https://www.polizei.de/Polizei/DE/Einrichtungen/ZAC/zac_node.html
- Local police
Reporting the scam on Truecaller will help prevent others from becoming victims.
- Internet safety concern: https://report.netsafe.org.nz/hc/en-au/requests/new
- Cyber security issues: https://www.cert.govt.nz/report/
- Phone: 0800 CERT NZ (0800 2378 69)
- Phone: 111 Immediate threat (emergency no)
- Phone: 105 (non emergency)
Reporting the scam on Truecaller will help prevent others from becoming victims.
Conclusion
Scammers impersonate reputable tech companies to gain trust and then use fear or urgency to deceive individuals into paying money or granting remote access to their devices to fix an issue that does not exist. They often contact people about a virus infecting their device or their system being hacked. It is crucial to stay vigilant and not fall for their fabricated scenarios. Also, installing apps like Truecaller is a reliable way to block spam calls and filter fraudulent messages through their SMS fraud detection feature.